🚀 HackiAI Now Detects, Explains, and Fixes Security Risks in IaC
Over the past few months, the number of attacks and breaches caused by infrastructure misconfigurations has increased dramatically.
Exposed AWS S3 buckets, overly permissive IAM roles, open ports, poorly managed secrets…
Most of these vulnerabilities don’t appear in production — they originate much earlier, in the code that defines the infrastructure.
Terraform, CloudFormation, Kubernetes manifests, Dockerfiles, Serverless Framework…
This code is the foundation of every modern system.
And that’s why today we’re announcing something important:
HackiAI now detects, explains, and fixes security risks in IaC.
🛡️ Why integrate IaC Security into HackiAI?
Until now, many teams relied entirely on external tools. The problem?
Some create vendor lock-in.
Others generate results that are hard to interpret.
Most tell you what’s wrong, but not how to fix it.
This leads to noise, frustration, and delays in the development lifecycle.
HackiAI changes that.
⚙️ What HackiAI now does with your IaC files
When an infrastructure or IaC file is sent to HackiAI (via CLI or API):
HackiAI performs a deep security scan.
It evaluates each finding in the context of your project.
It generates clear, understandable explanations of the risk.
It provides a recommended fix with real code examples.
It includes public, vendor-neutral references (AWS, GCP, Kubernetes, Docker).
It returns a clean, uniform, actionable report directly to the developer.
You get a complete, high-quality report right in your terminal —
before the issue ever reaches your remote repository.
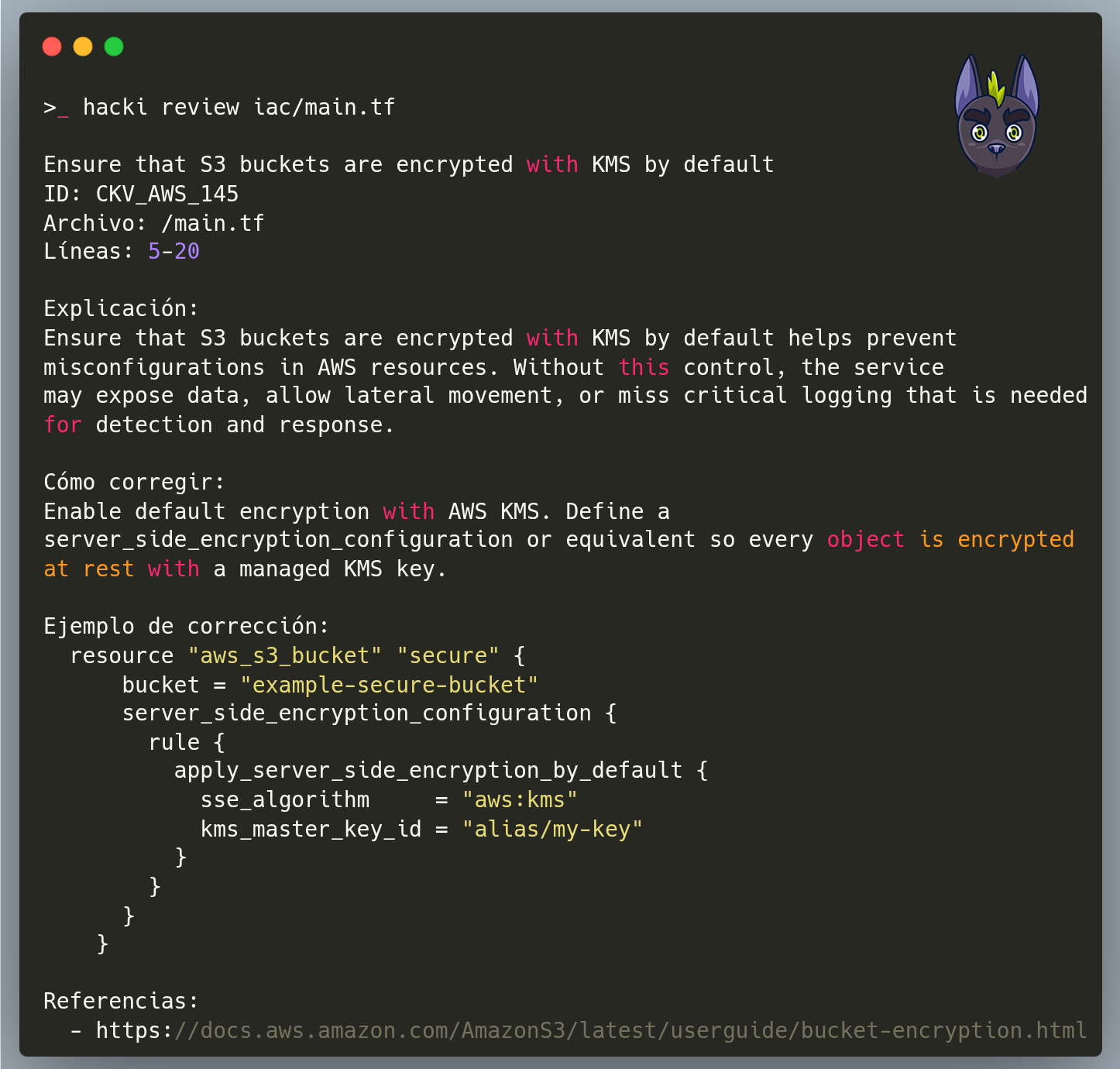
🧪 Real example: S3 bucket without KMS encryption
Instead of showing a generic message like:
“Bucket should be encrypted by default. Refer to cloud documentation.”
HackiAI now delivers:
A clear explanation of the risk
Why this exposes your data
Step-by-step instructions to fix it
A corrected code example
An official AWS reference (public and accessible to everyone)
This turns a simple “finding” into an immediate fix, without relying on multiple external tools.
🔍 Why this matters for your team
✔ Shift-left security, built into your workflow
Issues are detected long before they reach production.
✔ Less noise, fewer false positives
Developers receive clear, actionable information — no broken links.
✔ Faster onboarding
New team members better understand the project’s infrastructure.
✔ No vendor lock-in
HackiAI stays open, transparent, and independent.
✔ Solves the biggest problem in IaC scanning:
“I know what’s wrong, but I don’t know how to fix it.”
📁 Supported IaC File Types
HackiAI automatically detects and analyzes:
.tf,.tf.json(Terraform).yml,.yaml(Kubernetes, CloudFormation, Ansible).json(CloudFormation, ARM templates).template(CloudFormation)Dockerfileserverless.ymlHelm Charts
Pulumi (YAML/JSON)
Kubernetes manifests
Terraform modules and subfolders
If it’s IaC, HackiAI analyzes it.
🔚 Conclusion
With this release, HackiAI becomes a complete early-stage code analysis platform — from dependency and package security to critical infrastructure misconfigurations.
It’s a major step toward bringing DevSecOps practices to startups, small teams, and organizations that need security from the very first commit.